Quantum computers are a powerful and exciting technology that will change many things – for better or worse. The defense industry has a significant role and responsibility to protect its data and systems from quantum threats and to use the quantum benefits for their advantage and value. We have to be proactive and cooperative, so we’re ready for a quantum future.
Quantum 101
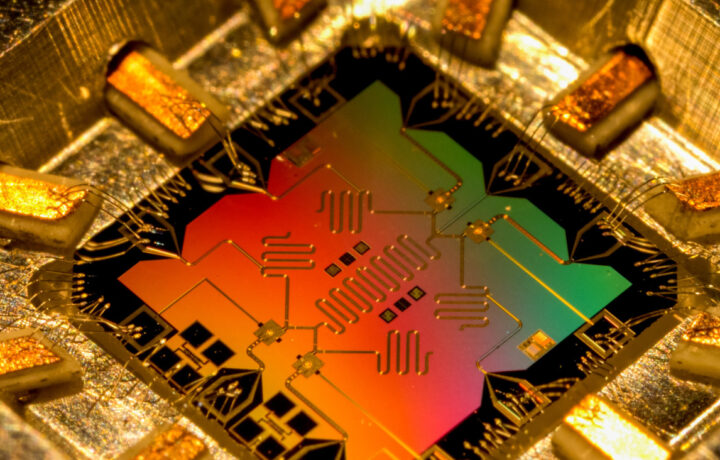
In case you’re new to the conversation, you might be wondering what it all really means and why you need to understand it. Quantum computers are a new kind of computer that uses quantum bits, or qubits, to represent information. Qubits are like switches that can be on, off, or both simultaneously. This is possible because qubits follow the rules of quantum physics, which are different from the rules of standard physics. Quantum physics is the science of tiny things, like atoms and electrons.
Quantum computers can do some things much faster and better than regular computers, such as finding the factors of a large number or simulating how molecules behave. Quantum computers can also do things ordinary computers cannot do, such as creating secret keys that are impossible to crack.
However, quantum computers also create a big problem. They can theoretically break the codes that regular computers use to protect data. Data is any information stored or sent online, such as passwords, messages, photos, or documents. Data protection is essential for the defense community because it protects data from hackers, spies, or thieves.
A Quantum Leap in Encryption
One way to protect data is to use encryption. Encryption is like a lock that scrambles data so only those with the key can open it. There are many kinds of encryption, but one of the most common is public-key encryption. Public-key encryption works by using two keys, one public and one private, that are related but not easy to guess. The public key can lock data, while the private key can unlock data. The public key can be shared with anyone, but the private key must be kept secret.
Public-key encryption is based on complex math problems that are easy to check but hard to solve, such as finding a big number’s factors or finding a number’s power uniquely. These problems are complicated for regular computers but easy for quantum computers. This means a quantum computer could unlock any data locked with public-key encryption without knowing the private key. This could be very bad for data protection because it could expose data that is supposed to be secret, such as military secrets, bank accounts, health records, or personal messages.
Solving The Problem
To solve this problem, people are working on new ways to protect data from quantum computers. These are called quantum-resistant encryption methods or post-quantum cryptography (PQC). These encryption methods are based on math problems that are hard for both standard and quantum computers, such as finding the shortest way in a maze or finding the original message from a messed-up message. PQC methods are not easy to make because they must be fast, secure, and reliable.
There are many PQC methods that people are trying to make, such as lattice-based encryption, code-based encryption, or multivariate encryption. Encryption methods use different kinds of math objects, such as grids, codes, or equations. Some examples of PQC methods are LWE, NTRU, or Rainbow.
There are also other ways to protect data that use quantum physics, such as quantum key distribution (QKD). QKD is a way to create and share secret keys that are guaranteed to be secure because any attempt to spy on them will change them and be noticed. QKD uses special devices that can send and receive qubits over a network.
Quantum Projects
The development and testing of PQC methods and QKD devices is an extensive and ongoing project involving many people and organizations from different fields, such as science, technology, business, and government. One of the main projects is the Post-Quantum Cryptography Standardization project by the National Institute of Standards and Technology (NIST), a government agency making standards for science and technology. NIST tries to choose and approve one or more PQC methods for each encryption, such as locking data, sharing keys, or signing data. NIST started this project in 2016 and plans to finish it by 2024.
Another big project is the Quantum Flagship, a 10-year, 1-billion-euro project by the European Union, a group of countries that work together. The Quantum Flagship is trying to make and use quantum technologies, such as quantum computers, sensors, and networks. The Quantum Flagship supports many projects related to PQC and QKD, such as PQCRYPTO, which makes and tests PQC methods, or OPENQKD, which builds and runs QKD networks across Europe.
A third big project is the Quantum Internet Alliance, a group of 23 European research teams and companies. The Quantum Internet Alliance is trying to build a quantum internet that can connect quantum devices, such as quantum computers, quantum sensors, and QKD devices, and enable new ways of using and sharing quantum information.
Changing to PQC and QKD is a challenging and vital task requiring cooperation and communication among many people and groups, such as researchers, developers, sellers, users, and regulators. The change to PQC and QKD will also affect the defense industry, which makes and sells things for the military, such as weapons, vehicles, or software. The defense industry needs to update its systems, products, and services to use PQC and QKD and ensure they are safe and reliable.
The Quantum-Defense Industry
The defense industry needs to start getting ready for the change to PQC and QKD as soon as possible. Here are four things defense leaders can doing to implement quantum changes.
- Check the current state of their data and systems and determine the possible risks and impacts of quantum attacks.
- Follow the progress and results of the PQC and QKD projects and try the PQC and QKD methods and devices that fit their needs and goals.
- Make and do a change plan that covers the technical, practical, and organizational aspects of the change, such as choosing and testing the PQC and QKD methods and devices, updating and installing the PQC and QKD software and hardware, teaching and informing the staff and customers, and managing the old and new systems.
- Join and work with the relevant people and groups, such as government agencies, industry associations, standards organizations, and research institutions, to share the best practices and lessons learned and to solve the common problems and issues of change.