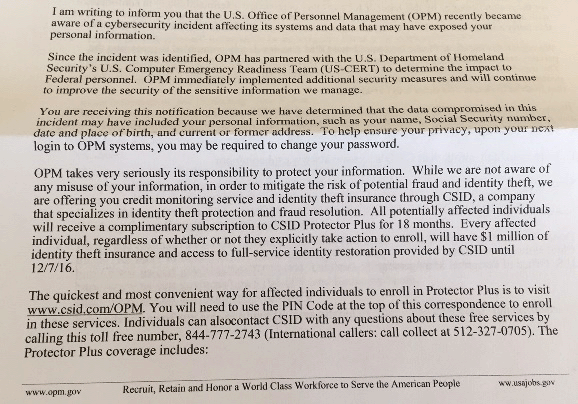
I just received my notification from OPM that my data was among that breached in the recent hack:
It looks just like any other notification you might get after your credit card is breached – the only difference is that in this case the data stolen is as extensive as the data that may be included on your SF-86. Which includes everything from your sex life to your drug history, and more. For all clearance holders and cleared companies, the breach is a sign of the government’s information security inadequacies. In the days since the breach I’ve heard from numerous uncleared candidates who say this is the very reason they don’t want to work for the government in the first place. Not good news for motivating the current workforce or attracting new cleared candidates.
As other authors have pointed out, the implications of the OPM breach are more complex than blackmail – which is really a blunt instrument of the spy game. Of greater concern is that China now has a blueprint for creating the perfect mole – particularly concerning what degree of foreign influence, debt, or other potentially disqualifying conditions allow an individual to make the cut. They can craft the perfect spy – by making sure he or she isn’t ‘too’ perfect, just the perfect blend of skills and associations to make an attractive candidate.
It’s likely China will keep a close hold on the data. This was a government-sanctioned attack not an Edward Snowden mission to paper the globe with classified information. But it’s clear OPM’s database was weak for years. If China wasn’t the only one with the data, or if they do decide to share it with their friends along the way, what other implications could there be?
Drugs, Dating, Ex-Wives and Extramarital Affairs
The SF-86 is more than a 127-page employment application, it’s basically a complete grilling on your personal and professional life, based on the 13 adjudicative criteria used to determine an individual’s trustworthiness with classified information. And the breach goes beyond a basic yes-or-no to questions, it includes supporting documentation, specifically the notes a background investigator may have taken in the course of subject interviews. If this has you cringing, there’s good reason. It’s the kind of information most of us wouldn’t want published. But if some people get their way, this kind of airing of cleared employee dirty laundry would probably be on the agenda – some people are already doing it for intelligence employees with LinkedIn profiles.
The only bright side for those affected by the breach is that it’s unlikely to hinder lives or work in a noticeable way – China isn’t likely to blackmail you, they’re also unlikely to sell your data to Russian crime rings. Vigilance with email and a keen eye toward any spear phishing scams are the biggest concern. For millennials like myself, we’ve already Facebook’ed and SnapChatt’ed our way into about 15-different types of blackmail, anyway.
No, the implications aren’t personal, although it may feel that way – they’re global, with significant national security implications.
For the government, the headaches are just beginning. We can hope it’s a wake up call, but there’s still a long way to go. The Federal Chief Information Officer is calling for a ‘cybersecurity sprint.’ I don’t think that will do it. Most government agencies require a complete security overhaul. OPM knew its databases were vulnerable and left them open for attack for years. We can hope that other government agencies and defense contractors in a similar position will take the drastic steps needed. And if you’re a cybersecurity professional, you can be certain Uncle Sam is hiring. Maybe you can join the team to help keep government secrets safe. They could use workers with the vision – and the skills – to get the job done. I, for one, will hope that breaches like these don’t scare more qualified applicants away.