The sensitive personal information of about 22.1 million people was affected in the recent OPM breach, officials announced. The breach included the background investigation data of individuals applying for positions with the federal government, as well as spouses, partners, and individuals listed as employers or references on the SF-86 application.
“It is a very big deal from a national security perspective and from a counterintelligence perspective,” FBI Director James B. Comey said at a meeting with reporters Thursday. “It’s a treasure trove of information about everybody who has worked for, tried to work for, or works for the United States government.”
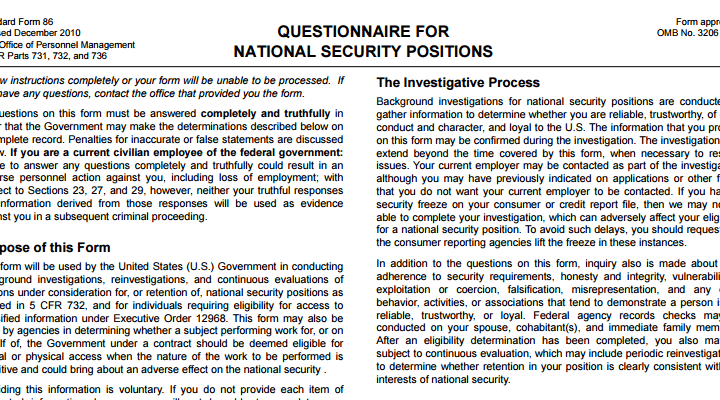
The majority of the affected individuals were security clearance applicants. Included in the 22 million figure are the individuals affected by an earlier announced breach of federal employee personnel files including social security numbers, performance evaluations, and more. The data about security clearance professionals included 1.1 million sets of fingerprints, as well as the user names and passwords applicants used to access the eQIP system.
OPM continues to draw fire for neglecting to notice the breach. It is believed that hackers had access to the security clearance system for at least six months before they were detected. Two federal employees’ unions have filed lawsuits against OPM, alleging that the agency violated workers’ constitutional rights by failing to protect their data. U.S. officials have thus far refused to confirm who is behind the attacks, although the Department of Homeland Security announced this week that it has a ‘leading suspect’ in the hack. Earlier reports have pointed the finger directly at China, but the White House and government officials remain mum.
The effects of the hack will be far reaching, with many officials concerned about how this will affect American intelligence gathering. There are also significant personal security concerns for cleared professionals who have had their SF-86 details, user names and passwords, and other data ripe for use in a spear phishing attack, compromised.