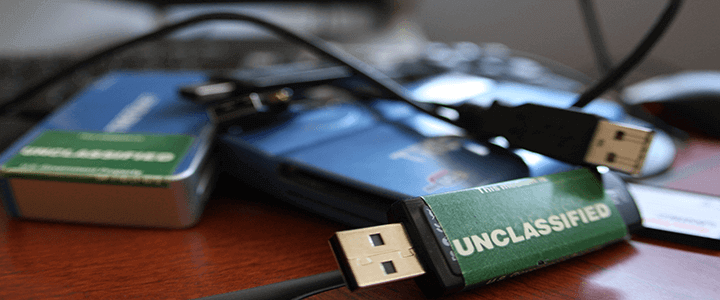
How many times have we copied a report, presentation or spreadsheet onto a USB-drive or other portable media? If you are anything like me, hundreds. Now, in each instance, did you process through your mind, what happens if I lost this USB-drive? No? Nor did I. I was more interested in making sure I had my presentation or important papers available in the event my laptop gave up the ghost at zero-hour.
But I also had the luxury of having been indoctrinated into the world of Murphy’s Laws at an early age during my career as an intelligence officer, which makes certain, “If anything can go wrong, it will.” And for this reason, I either sanitize what is going on the portable media or encrypt the data, so that when it goes out of my control (and Murphy tells me it is a “when” not an “if), I have a non-event.
Clearly, this was not the thinking within the security detail at London’s Heathrow Airport and Buckingham Palace. The Queen’s personal security was potentially compromised when a USB-drive was found lying on the ground near Kensal Green cemetery.
The Register (UK) tells us that the individual who found the USB-drive took it home and did what every lesson in cyber hygiene tells us not to do, he plugged it into his computer. Fortunately for this individual the USB-drive wasn’t loaded with malware, but what it was loaded with was a treasure trove of security documents pertaining to London’s Heathrow Airport, and Her Majesty’s route through the airport. Specifically, 76 folders, with 174 documents totalling 2.5GB of data. The documents carried UK classification markings of “restricted” and “confidential” – indicative of their sensitivity.
How bad is bad when a USB-drive goes missing?
These 76 folders of sensitive information according to the Mirror, included maps, videos and documents, all of which put the airport and the Queen in danger. Information included:
- Route used by the Queen when using Heathrow, to include security measures in place to protect her.
- What IDs are need to access restricted areas, including those used by undercover law enforcement.
- Timetables of patrols put in place to thwart terror attacks including suicide bombers.
- Maps indicating the exact location of CCTV cameras.
- Maps of the network of tunnels and escape shafts linked to the Heathrow Express train.
- Routes and security safeguards used by various Cabinet Ministers and foreign dignitaries.
- Details on the ultrasound system which monitors the airport perimeter and runways for anomalous activity.
The Mirror continues, how police sources are concerned the treasure trove of data has been shared on the “dark web” and thus, ‘the fear is that this information could have been downloaded and disseminated God knows where.”
Heathrow’s error is your opportunity
Clearly Heathrow is in damage assessment mode. They’re adjusting their security protocols and those for the Queen and others. Unless someone steps forward and says, “yes, I downloaded those documents onto a USB-drive” they will be hard pressed to determine whether or not this is an act of dangerous mischief or of piss-poor security on the part of an insider with access.
What can you or your colleagues copy off your devices? Is there a data loss prevention infrastructure in place to alert when sensitive information is off-loaded to a portable device? If there isn’t, have that conversation with the IT security team. And make sure when you fill that USB-drive up with sensitive data, you are handling it appropriately.