I’m an old school, CIA Cold War veteran. I spent many of my years at home and abroad working within a shielded enclosure, including in some of the most technologically hostile environments – USSR for example. Cold War history books and espionage lore are replete with examples of the KGB and then the FSB attempting to attack U.S. government entities. When facing off against such an adversary one knows they are coming at you with their A-game, every day. The USSR’s KGB, on their home turf, would bring everything they had, knowing that the target’s ability to adjust their defenses was limited by both geography and logistics.
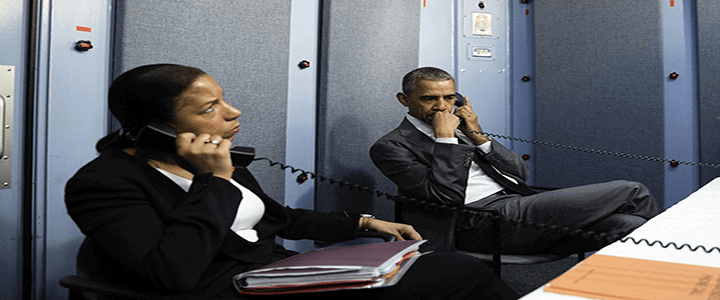
Shielded Enclosure — Sensitive Compartmented Information Facility (SCIF)
Shielded enclosures may be a SCIF or a part of a SCIF. They exist, as we have explained in our piece “What is a SCIF“, as a “room or series of rooms that have been designed and constructed to prevent outside access to the information being discussed in them. The Federal government has a set of standards, spelled out in Intelligence Community Directive 705/IC Technical Specification.”
“The SCIF is built to prevent the transmission of sound through the walls, floor or ceiling and through HVAC. All telephone, electrical power, security systems, data and emergency systems equipment must be dedicated to and contained within the SCIF,” they note. The room may be enclosed in a Faraday cage or other means of preventing electronic transmissions from the space.”
There you have it–the SCIF/Shielded Enclosure is designed to keep the signals inside and not allow an adversary externally to penetrate the “enclosed area” for the purposes of intelligence collection.
Reasons why the answer is a Shielded Enclosure
- Classified Information – your Facility Security Officer, working with the cognizant security authority and contracting office will determine if your contract requires a shielded enclosure for your entity to handle/access the U.S. government’s classified information. The facility security clearance outlines the Communications Security (COMSEC) requirements.
- Internet of Things – We are tethered to technology. I know I am. These devices come with us into our work spaces, vehicles, homes, etc. If you’re accessing your company’s sensitive (but perhaps not classified) information, holding discussions, and making decisions and have your devices present, are you an Operational Security (OPSEC) threat? Could an adversary who compromised the “smart watch” or “smart phone” eavesdrop or remotely activate your built in digital camera? Secretary of Defense Mattis placed a marker down in February after it was leaked that he is considering a ban on cellular phones and personal electronic devices in the Pentagon.
- Isolated systems aren’t enough – Many defense contractors and companies involved in cutting-edge research have opted to create technological enclaves or air-gap systems. In a recent Wired piece, Israeli security researcher Mordechai Guri demonstrates how he has mastered the exfiltration of data from an air-gapped device using the electromagnetic field provided by those smart phones.
OPSEC is in your hands
In closing, OPSEC is always personal. Your smart devices can be a boon and they can also be an intelligence gold mine, or a counterintelligence headache. I know from my broad experience both in government and the private sector, you are entrusted with sensitive information required to perform your duties. The expectation is that you will, because you are trusted, adhere to the requirement to protect the information (at all times). Sometimes, the best defense is to block out that which we cannot control, and use the shielded enclosure.