Hundreds of thousands of Microsoft customers are vulnerable to foreign actors, believed to be China cybercriminals identified as HAFNIUM, as Microsoft Exchange Servers are exploited.
From March 3 through 5, Microsoft has been issuing security updates for their family of Microsoft Exchange Servers from 2013, 2016, and 2019 to close previously unidentified vulnerabilities which were being exploited China’s HAFNIUM group (Microsoft security update). The security update emphasizes that entities with more than one Exchange Server should prioritize updating to those which are external facing.
White House – Unified Coordination Group
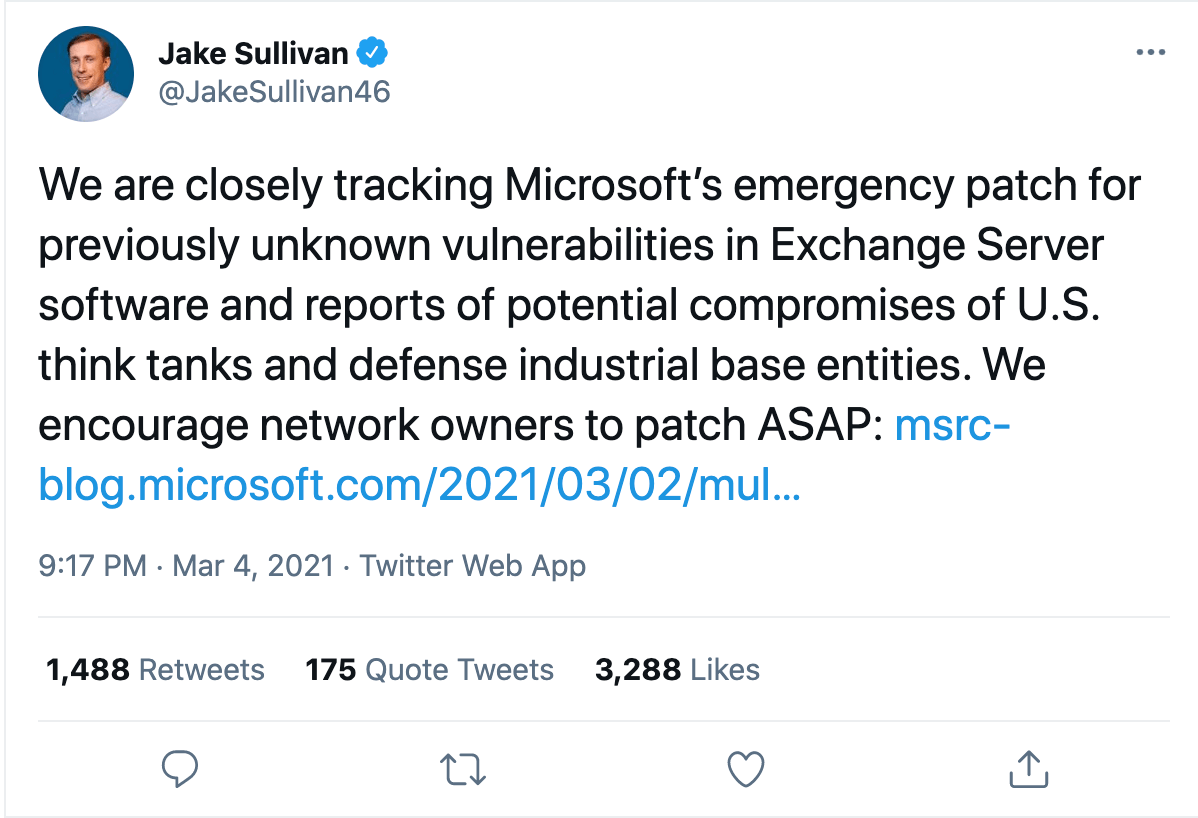
The White House is forming a “Unified Coordination Group” (UCG) , initiated by the National Security Council. The UCG will be comprised of the FBI, CISA, and others (tbd). White House press secretary told media on March 5, “everyone running these servers — government, private sector, academia — needs to act now to patch them.” This admonishment followed, national security advisor, Jake Sullivan’s March 4 tweet:
HAFNIUM – thousands affected
Modest estimates put the number of Microsoft Exchange Servers in the United States affected to be in the neighborhood of 30,000, with global estimates to be greater than 250,000. Microsoft advises they are working closely with CISA to ameliorate this threat, and will be updating all of their family of servers in the coming days, and are issuing updates as they become available.
Those entities which have not updated their servers are knowingly placing their servers and email at risk as the identified vulnerability is being exploited at breathtaking speed. Krebs on Security reports that of those 30,000 servers in the United States, “a significant number are supporting small businesses, towns, cities, and local government.” Krebs notes how the Chinese unit has “seeded hundreds of thousands of victim organizations worldwide with tools that give the attackers total, remote control over the affected system.”
CISA & U.S.-CERT on HAFNIUM
CISA issued an Emergency Directive (21-02) providing guidance to Federal Agencies (not including “national security systems” nor the Department of Defense). The guidance which mirrors and references multiple US-CERT (Cyber Emergency Response Team) notes that the exploitation does not currently affect Microsoft 365 or Azure Cloud. Successful exploitation, as indicated supra, “allows an attacker to access on-premises Exchange Servers, enabling them to gain persistent system access and control of an enterprise network.” Government agencies and contractors supporting government entities are required to immediately apply Microsoft patches, and follow a host of steps in order to preserve the state of their servers for forensic inspection and analysis by CISA.
A Word For FSO’s
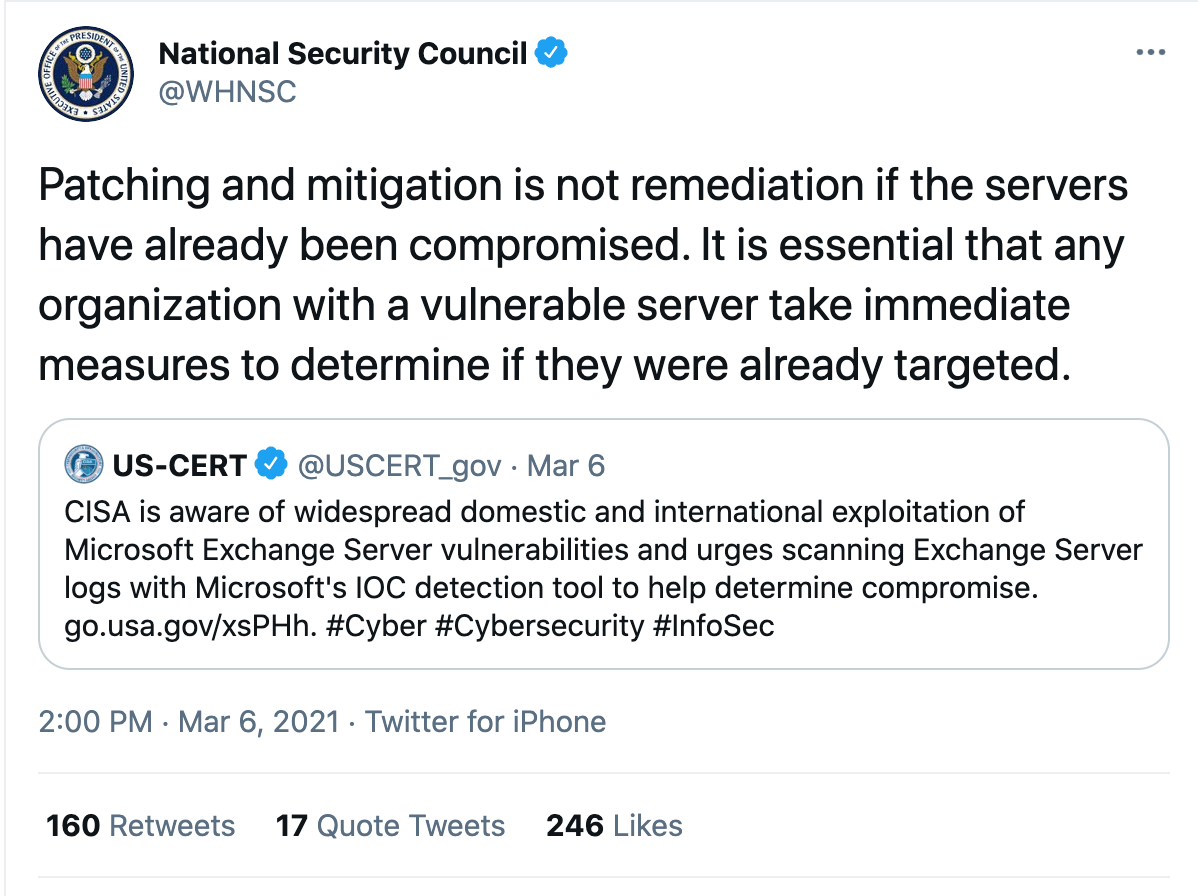
The National Security Council, via a tweet, reminds that patching is not remediation for those entities which have already been compromised. Therefore, before updating/patching, FSO’s should direct their cybersecurity teams to adhere to the CISA Emergency Directive and U.S.-CERT Alerts which contains instructions on how to forensically preserve and mitigate.
In addition, everyone should check out the Microsoft blog which offers a comprehensive explanation of how the HAFNIUM operates from China to compromise U.S. systems. They remind us, “Even though we’ve worked quickly to deploy an update for the Hafnium exploits, we know that many nation-state actors and criminal groups will move quickly to take advantage of any unpatched systems. Promptly applying today’s patches is the best protection against this attack.”