On July 19, a sealed indictment of four Chinese Ministry of State Security (MSS) officers was unsealed and the individuals were charged with the hack of victims in the United States and least 11 other countries. The court documents and Department of Justice (DoJ) announcement highlight the modus operandi used by the MSS officers, to include their cover-for-action mechanism which served to obfuscate their MSS affiliation.
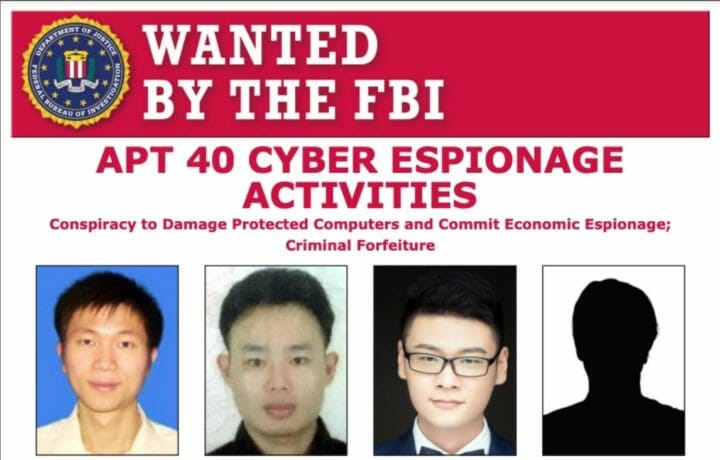
FSO’s will want to review the indictment of Zhu Yumin, Wu Shurong, Ding Xiaoyang and Cheng Qingman for details on how this group of individuals, known as “APT 40” conducted their cyber espionage activities. For those FSO’s whose footprint includes access to ITAR and EARS information access and control, particular emphasis should be made to inform their trusted and approved foreign partners on the Chinese M.O.
“These criminal charges once again highlight that China continues to use cyber-enabled attacks to steal what other countries make, in flagrant disregard of its bilateral and multilateral commitments,” said Deputy Attorney General Lisa O. Monaco. “The breadth and duration of China’s hacking campaigns, including these efforts targeting a dozen countries across sectors ranging from healthcare and biomedical research to aviation and defense, remind us that no country or industry is safe. Today’s international condemnation shows that the world wants fair rules, where countries invest in innovation, not theft.”
Chinese global hacking campaign 2011- 2018
To say China’s been eating their target’s lunch would be an understatement as more and more revelations meet the eye on their repeated successes in penetrating government, academia, and industry for cyber espionage purposes, even though in 2015, President Xi of China signed an accord which clearly stated that China would be standing down on the theft of intellectual property.
The court documents highlight how the MSS created a front company, “Hainan Xiandun Technology Development Co., Ltd” which was ostensibly a “big data security, security situational awareness, and security technological research … committed to exploring the development of cutting-edge science and technology.” Their successes evidenced they were true to their word, they developed cutting-edge techniques to further their cyber-espionage goals.
The MSS tasked the team with the requirement to develop malware and vulnerability evaluation methodologies for use against foreign governments, companies, and universities.
The Hainan Xiandun company clearly understood the value of the total compensation package and rewarded their employees (hackers) for their efforts. The indictment indicates that the teams received training, salary, paid vacations, and MSS performance rewards. The latter indicative of their success in achieving their tasking requirements.
What did CHINA steal?
The indictment highlights how they successfully targeted Ebola research; dual-use technologies (to include: “submersibles, autonomous vehicles, specialty chemical formulas, and genetic-sequencing technologies.”); Government entities in the United States and elsewhere; Airlines and companies supporting the global aviation industry; and the U.S. National Institutes of Health.
Given the current global pandemic involving COVID-19 which has its point of origin associated with Wuhan, China, the efforts of the Hainan Xiandun team no doubt raised a few eyebrows when discovered. The indictment notes how Zhu Yunhim was an OSINT collector targeting the U.S. CDC and the U.S. Department of State Biosecurity Engagement Program. Their efforts to initiate and succeed in the cyber espionage attacks against U.S. research entities to include the NIH, all which were involved in virus research evidences China’s interest.
As this author noted in his own book, Secrets Stolen, Fortunes Lost (Syngress 2008) the theft of intellectual property is the equivalent of sucking the life’s blood from companies and infusing them into the thief’s. China’s government research and development centers were the direct beneficiaries of the stolen information. These entities could reach out and fund domestic industry or research without the expense of the initial groundbreaking work conducted by the targeted research and development efforts abroad.
Not surprising, it is oftentimes cheaper to steal a technological trade secret than to develop it, and the investment China has placed on the latter should serve as evidence for every FSO and the C-Suite they brief and support.