From Alexa controlling our TVs to Siri providing directions, we’re increasingly becoming dependent on smart devices. The “smart home” of the future is now a reality, as robot vacuums go on dirt patrol and other smart devices are there to make our lives easier. A dark side of the reliance on the Internet of Things (IoT) and accompanying technology that comes with it is that it is all could potentially create new exploits for hackers, cyber criminals and other bad actors.
The plethora of devices that are being offered by competing manufacturers also means that there is no easy solution when it comes to cybersecurity. And since these devices could be on a home network, any insecure piece of equipment could be the weak link in an otherwise secure system.
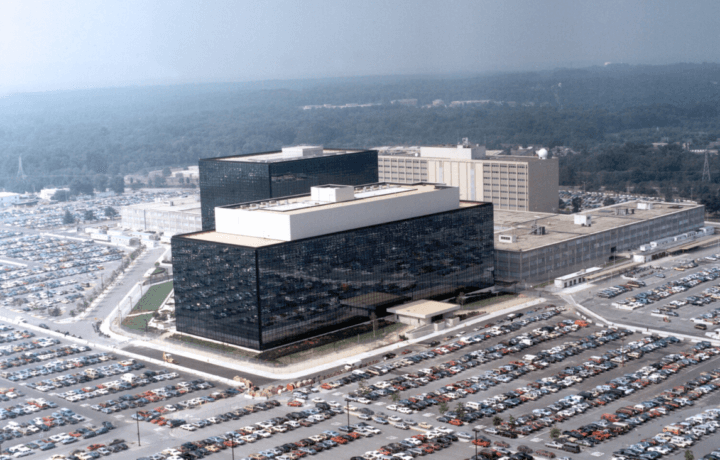
To address these potential threats – which will only increase as more devices are “connected” – researchers at the University of Missouri College of Engineering have received a two-year, approximately $500,000 cybersecurity research grant from the National Security Agency (NSA) to develop a flexible, add-on security feature that allows different types of smart devices to intelligently learn from past cyberattacks while having a minimal need for direct human intervention.
The grant, Automated and Intelligent Threat Detection and Defense of Future IoT Edge/Cloud Systems, was awarded by the NSA’s National Centers of Academic Excellence in Cybersecurity, through their Cybersecurity Research Innovation 2021 Program.
Prepared Response
The researchers have sought to incorporate a collaborative network among the developers of these devices for sharing solutions in order to better respond against potential attacks in the future.
“It’s plausible that these devices can be compromised and used to launch large-scale attacks,” said Prasad Calyam, director of the Center for Cyber Education, Research and Infrastructure at the University of Missouri and the principal investigator on the grant.
“For instance, we have seen hackers take control of people’s home-based internet routers to launch massive attacks against major internet providers in recent years,” added Calyam “Our challenge is developing a way to automate the process of securing smart devices, because it is not practical to do so manually at the large scales of deployment we are seeing in homes, businesses and government — there are no screens that can display a security problem or prompt a user to update the software on many of these devices.”
One issue is that commercial developers, even those at large consumer electronics firms, may not yet have the security techniques needed to keep up with the changing nature of cyberattacks, which furthers the need for this type of research and related technologies.
“Each device can use different kinds of security protocols, so determining which is the right approach to protect a device from unauthorized access is not clear because often times we don’t fully understand the changing threat being presented, and we don’t learn how a particular security approach will be able to handle that changing threat,” explained Calyam.
“Having too much or too little security is not ideal in response to a threat, so the key aspect in our approach is being able to use machine learning techniques to customize the response, while coupling that with use of trusted threat intelligence platforms based on blockchain to adapt to the need presented by the attack,” he noted. “We believe our approach will help make smart security better for smart devices.”
Smarter Security for Smarter Devices
To help protect our smart devices, it will require more than just another firewall, and researchers are exploring ways of using other smart technology.
“We employ machine learning techniques all the time to improve predictions for when one or another activity looks malicious, so the ‘learning’ part of this initiative is not what’s novel,” said Jim Purtilo, associate professor of computer science at the University of Maryland.
“What sounds new to me is the level of autonomy they are trying to build into devices so effective predictions can be made, and then applied, out in the wild,” Purtilo told ClearancesJobs. “IoT products are commonly small devices dedicated to very specific tasks, and while they’re fully connected – that’s the ‘I’ part of ‘IoT’ – accessing them to manage or configure behavior is not as easy an operation as with a full-featured system.”
The scale is what could be daunting however.
“A modern smart home might incorporate many dozens of such devices, and we need good engineering just to get them all to cooperate amicably; the obvious next step is to find a way for them to cooperate in common defense too.
It will be quite a challenge,” explained Purtilo. “The principle investigators need to find an efficient way to harvest prediction data from a host of diverse architectures, develop prediction algorithms that are effective in spite of the device heterogeneity – ‘one size fits all’ methods clearly won’t work – and yet not at the same time open a wider attack surface on any device. It’s an interesting project and I hope to see them make good progress in this important area.”
The fact that the NSA is the agency that has awarded the grant is also notable.
“It has been pretty common for the U.S. three-letter agencies to invest in start-ups who have an idea that can help them,” said technology industry analyst Roger Entner of Recon Analytics.
“I-Q-Tel is the most high profile of these Intel VC funds,” Entner told ClearanceJobs. “In general, the past is the best predictor of the future, especially because consumers are notoriously slow in fixing known vulnerabilities, but especially in hacking you need to find the holes nobody has found yet and plug them before the bad guys show up.”