In May 2019, the United States Department of Defense (DoD) announced that it was developing a new cybersecurity certification for DoD contractors. The new standard, called the “Cybersecurity Maturity Model Certification” (CMMC), was meant to address cybersecurity deficiencies in the defense industrial base and to secure the supply chain.
CMMC intends to ensure that defense contractors and subcontractors are compliant with existing information protection requirements for federal contract information (FCI) and controlled unclassified information (CUI) and are protecting that sensitive unclassified information at a level commensurate with the risk from cybersecurity threats, including advanced persistent threats.
CMMC was also developed to be semi-automated and more importantly, cost-effective, so that small businesses could still achieve at least a level-one certification within the program. Since the announcement of the program in 2019 many have wondered when the program would move from idea to proposed rule, with much speculation on if the program would remain on track – or even ever move forward at all.
The DoD CMMC program is now fully defined by the current rulemaking in the 32 CFR regulatory process.
CMMC Revisions Now in 60-day Comment Period
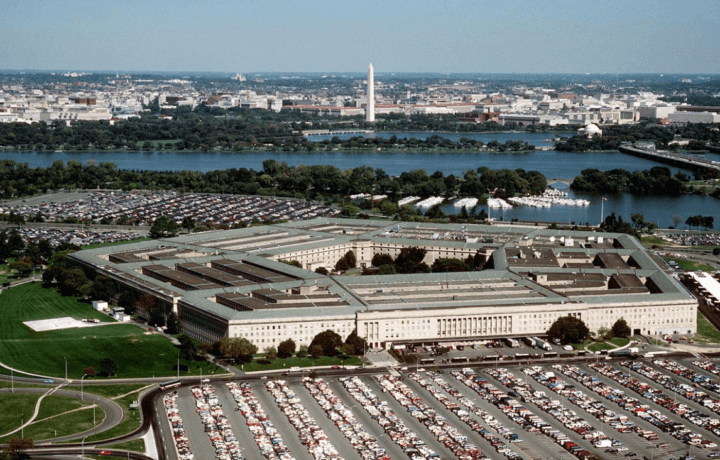
This Tuesday the Pentagon published for a 60-day comment period for a proposed rule for the CMMC program, which revises certain aspects of the program to address public concerns in response to DoD’s initial vision for the CMMC 1.0 program, as originally published in September 2020.
The Pentagon further noted that with its streamlined requirements, the CMMC program now provides for simplified compliance by allowing self-assessment for some requirements; while maintaining priorities for protecting DoD information. In addition, the requirements are meant to reinforce cooperation between the DoD and industry in addressing evolving cyber threats.
“As discussed in the proposed rule, CMMC requires cybersecurity assessment at only three levels, starting with basic safeguarding of FCI at CMMC Level 1,” the DoD explained. “General protection of CUI will require assessment at CMMC Level 2, and a higher level of protection against risk from advanced persistent threats will require assessment at CMMC Level 3.”
In addition, the rule will also add flexibility by allowing for limited use of plans of action and milestones and a government waiver request process.
The Pentagon has estimated that the overall program costs will be reduced by allowing for self-assessments for Level 1 and some Level 2 assessments, while further minimizing cost to industry for Level 3 assessments by having Government assessors from Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) conduct these assessments.
Moreover, the DoD suggested that CMMC aligns directly with the cybersecurity requirements described in National Institute of Standards and Technology (NIST) Special Publications 800-171 and 800-172.
Building on the CMMC 2.0
The new rules also build on the CMMC framework 2.0, which meant to reduce the security certification tiers from five to three while it also removed the third-party assessment requirement for level one and part of level two, which in turn allowed contractors to return to self-attestation.
It was seen as providing incremental improvements, and wasn’t actually the final word in cybersecurity for the DoD. Some have even questioned whether it is even the step in the right direction.
In addition, as noted by the Office of Information and Regulatory Affairs at the Office of Management and Budget within the Executive Office of the President, “DoD considered and adopted several alternatives during the development of the interim rule that reduced the burden on small entities and still meet the objectives of the rule. DoD will consider similar alternatives for the amendment rule. One alternative considered includes exempting contracts and orders exclusively for the acquisition of commercially available off-the-shelf items.”
OIRA further noted that the theft of intellectual property and sensitive information from all U.S. industrial sectors due to malicious cyber activity threatens economic security and national security, and that malicious cyber actors have and continue to target the defense industrial base (DIB) sector and the Pentagon’s supply chain.
“These attacks not only focus on the large prime contractors, but also target subcontractors that make up the lower tiers of the DoD supply chain,” OIRA warned. “Many of these subcontractors are small entities that provide critical support and innovation. The aggregate loss of intellectual property and certain unclassified information from the DoD supply chain can undercut U.S. technical advantages and innovation, as well as significantly increase risk to national security.”