After a nearly six-month hiatus, the Defense Office of Hearings and Appeals is once again publishing the results of the cases they adjudicate. In the transition to DoD systems, cases weren’t posted online for the first half of the year. Now, with 2021 decisions rolling in we can once again get a glimpse into defense security clearance adjudications and who loses and wins in the fight for eligibility. And as expected, misuse of IT systems has popped into the 2021 appeals cases right out of the gate.
We’ve predicted here before that we will likely see an uptick in security clearance denials based on misuse of IT systems, with the flood of folks who began working from home during COVID and the patched IT solutions some embraced to make it work. The following case isn’t COVID related (the suspicious IT activity started in 2014), but it signals what can happen if you use your workplace device for something you shouldn’t.
True or False: It’s Okay to Use Your Workplace to Device for Cybersecurity Coursework – It’s Considered Professional Development
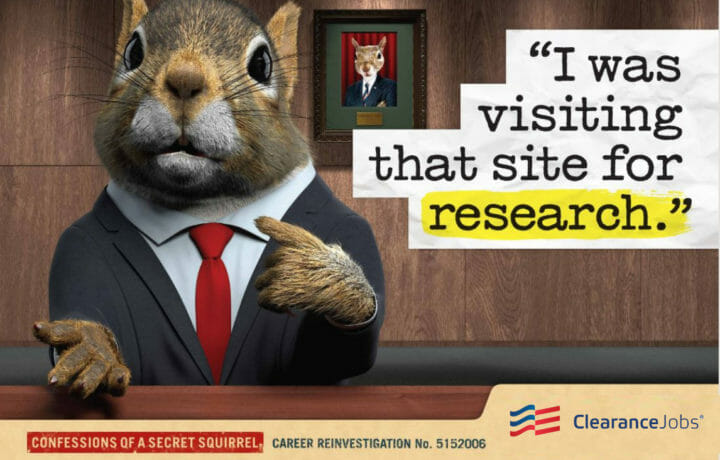
In this case the applicant was a mid-level IT professional working for a defense contractor. In 2014, he was terminated from a job due to a series of egregious IT violations, which included initiating a peer-to-peer connection with a remote host, researching computer hacking and password cracking, downloading pirated software onto his workplace device, and other violations. The applicant tried to use the ‘research’ defense, noting the work was related to a certificate for ethical hacking he was looking to pursue.
That defense didn’t hack it for the applicant’s employer at the time, who noted any need for this type of knowledge for his current job was rare, that the amount of hacking material was ‘disconcerting’ and cited poor judgment. The applicant lost that position, but was able to find another IT position and has been working for a defense contractor for the past two years.
In the applicant’s security clearance application, the termination was noted and the IT violations were discussed. Despite the more than five years that have passed since the violation, the government found that the severity of the violations was enough of an issue to deny eligibility today.
False: Research is not a good defense for violating IT policies
The applicant had numerous strikes against him, particularly the severity of the violations and the fact that he had tried to conceal or cover up his activity in some instances. Reliability and trustworthiness are critical aspects of the security clearance determination process. In this case, the applicant also likely hurt his case by his various attempts to justify or explain away his violations. A common thread in those who have committed espionage or sold secrets was a sense of ‘entitlement’ to the information, access, or illegal acts committed. Sometimes, it’s better to just accept responsibility for a violation. Sometimes an explanation can be a mitigating factor, sometimes it contributes to an overall picture of someone who breaks IT policies – and thinks it’s okay.
The final takeaway is that as an IT professional, this individual should have had a clear understanding that his pirated software, password hacking attempts and other violations would be discovered by his employer. All of these activities were conducted on a workplace device. With more individuals than ever taking their work home in the form of a company or agency laptop, it’s important that what happens at home, doesn’t stay there – but is traveling to your IT department. That doesn’t mean they’re personally monitoring every visit to Amazon, but it does mean you’ll need to do your certified ethical hacking ‘research’ on your own time.